Identity and Access Management
Strengthen the cybersecurity posture of your digital business by implementing user management and access control of your business applications through resilient, trustworthy IAM Solutions
DigiTaiken is a proud OKTA partner
Access Granted
Access Granted
To Access Cloud

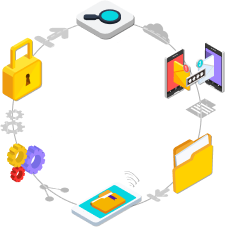
Why Organizations need Identity and Access Management?
Identity thefts and unauthorized access are real threats. Identity thefts and unauthorized access are threats.
Organizations are becoming vulnerable to the identity gaps and inconsistencies caused by traditional security approaches in the modern digital era. To mitigate these risks, organizations must enforce a strong IAM program that empowers and covers them against all associated risks.
$100 billion
has been saved preventing identity threats65%
Digital companies are implementing IAM5 Times
Increase in data and access security strength through IAMWhat We Do
DigiTaiken is a proud Okta partner, delivering an Identity and Access Management portfolio that encompasses a wide range of solutions and services. We take a three-step approach to Identity & Access Management Solutions.